Windows giant extends passwordless tech to everyone else
Jessica Lyons Thu 2 May 2024 // 23:03 UTC
Microsoft today said it will now let us common folk — not just commercial subscribers — sign into their Microsoft accounts and apps using passkeys with their face, fingerprint, or device PIN.
The additional support for Microsoft consumer accounts works across Windows, Google, and Apple platforms, and Redmond described the move as a step closer to its 10-year dream: "A world free of passwords."
As of Thursday, people can sign into their Microsoft accounts using passkeys via desktop and mobile browsers, and we're told mobile app support is coming soon.
The timing isn't
coincidental. Today is also World Password Day, which, albeit a made-up
holiday, usually marks the occasion for tech companies to brag about what they
are doing to move away from requiring or encouraging users to remember or jot
down in some way unique, strong passwords for each app and online service they
use.
True to form,
Google also marked the occasion by proclaiming that its year-old passkey
support hit a milestone.
"Today, we
announced that passkeys have been used to authenticate users more than 1
billion times across over 400 million Google Accounts," project managers
Sriram Karra and Christiaan Brand said.
When Microsoft
rolled out Windows Hello and Windows Hello for Business in 2015, it was
detecting about 115 password attacks per second, or so says Redmond's Vasu
Jakkal, corporate VP for security, compliance, identity and management, and Joy
Chik, president for identity and network access.
As of 2023, that
number had increased 3,378
percent to more than 4,000 per second.
"Password attacks are so popular because they still get results," Jakkal and Chik wrote in a blog post announcing the passkey support.
"It's
painfully clear that passwords are not sufficient for protecting our lives
online," they said. "No matter how long and complicated you make your
password, or how often you change it, it still presents a risk."
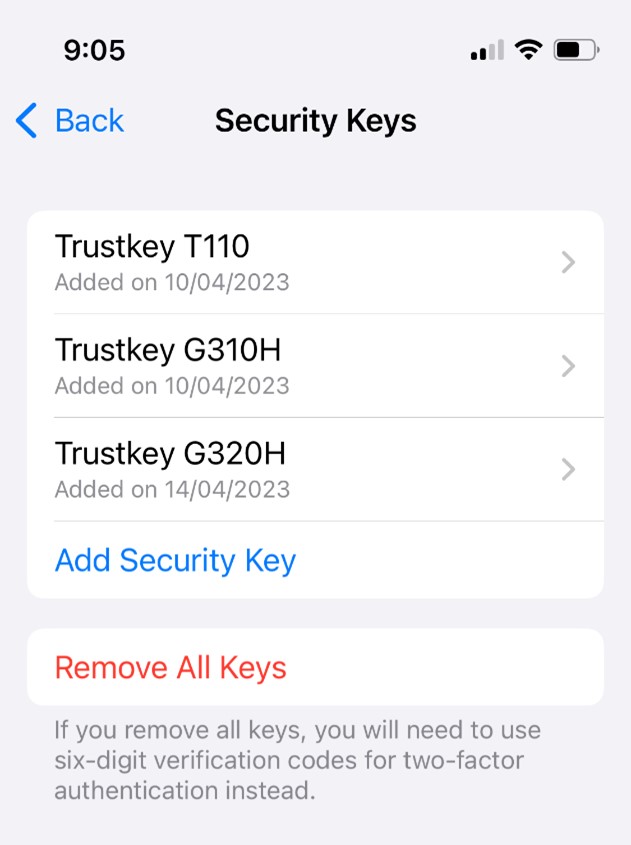
Passkeys are based
on a FIDO alliance standard that's
supported by Apple, Microsoft and Google. Think of them as password
replacements.
The tech, simply
put, works like this: When you create an account for a website or app, your
device generates a cryptographic public-private key pair. The site or app
backend gets a copy of the public key, and your device keeps hold of the
private key; that private key stays private to your gear. When you come to
login, your device and the backend authentication system interact using their
digital keys to prove you are who you say you are, and you get to login. If you
don't have the private key or can't prove you have it, you can't login.
Your device can
secure that private key locally using something like a biometric face scan, a
PIN, or a fingerprint. Thus if someone wants to break into your account,
they'll need your device and that secret PIN or biometric scan to unlock the
private key (or somehow get a copy of the private key). This is seen as more
secure than making people remember or store passwords, and ensures a unique
key-pair per account. For those wondering about multifactor authentication,
it's kinda baked in: Typically a crook will need to get hold of your physical
device, and your secret or physical part of you to access the private key.
"Because this
key pair combination is unique, your passkey will only work on the website or
app you created it for, so you can't be tricked into signing in to a malicious
look-alike website," Microsoft explained. "This is why we say that passkeys
are 'phishing-resistant.'"
Ultimately, they
aim to simplify security for users by relying on a face or fingerprint scan
instead of requiring people to remember a unique 47-character password for
every damn app and website they access that includes uppercase letters,
lowercase letters, numbers, special characters, and the name of your first pet
but only if they were a parakeet.
"The best
part about passkeys is that you'll never need to worry about creating,
forgetting, or resetting passwords ever again," according to Jakkal and
Chik.
To be fair, this
is probably an overstatement. Criminals are a cunning bunch, and they may find
ways to break this latest approach — and we're not talking about cutting off
people's fingers or faces.
But on this World
Password Day, here's hoping we can bask in the simplicity and security of
passkeys for at least another year.










.jpg)






.jpg)